In this tutorial you are going to learn how to secure your web application using the Spring Security including user authentication, authorization and more.
Spring Security – Introduction
Spring Security is a customizable authentication framework. It is the standard when it comes to securing Spring-based applications. It provides both authentication and authorization. Authorization is also known as “access-control”.
The core building blocks in Spring Security
- SecurityContextHolder: Associates the current SecurityContext with the current execution thread. It holds the information of the SecurityContext that is currently interacting with the application. The security context information is stored in a ThreadLocal object which makes it available to all members that are running in the current thread.
- SecurityContext: Interface that defines the minimum security information associated with the current thread of execution. In other words, it holds the Authentication object and request-specific security information.
- Authentication: Represents the token that is needed for an authentication request. Once the request has been authenticated, the token will usually be stored in a thread-local SecurityContext managed by the SecurityContextHolder. After the user authentication, the Authentication object is built by using the UserDetails object after which it is stored in the SecurityContextHolder.
- UserDetails: Provides the core information about the user.
- UserDetailsService: Loads specific user data. It is an interface which allows to load user-related information from the database. The interface requires only one read-only method which simplifies support for new data-access strategies.
- GrantedAuthority: Usually loaded by UserDetailsService. Represents the authority granted to an Authentication object.
Authentication
Authentication (as mentioned earlier) represents principal information (user, device, external system, etc.) that interacts with the application. When dealing with user authentication, the username and the password are retrieved from the incoming request and then are made an instance of UsernamePasswordAuthenticationToken. This token then is passed to an AuthenticationManager which validates the principal identity against the one in the database. If the authentication has been successful, AuthenticationManager returns an Authentication object that stores the principal details. Finally, the authentication object is populated into the security context with help by SecurityContextHolder method.
Let’s take a look at how the AuthenticationManager interface looks like:
public interface AuthenticationManager {
Authentication authenticate(Authentication authentication)
throws AuthenticationException;
}
As you can see, it only has 1 method. However, this one mehtod can be used to accomplish 3 things:
- return an Authentication (refer to the text above)
- throw an AuthenticationException
- return null
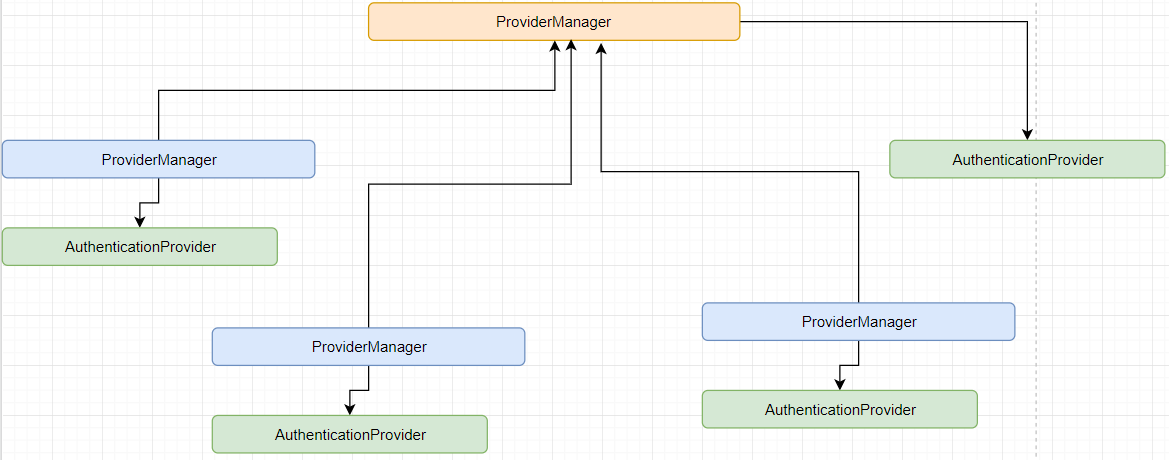
The AuthenticationManager commonly serves an implementation to ProviderManager which then delegates to a chain of AuthenticationProvider instances. The AuthenticationProvider is much like AuthenticationManager only it has 1 more method:
public interface AuthenticationProvider {
Authentication authenticate(Authentication authentication)
throws AuthenticationException;
boolean supports(Class<?> authentication);
}
Authorization
Authorization’s job is to decide whether the user is allowed to access a given resource, in other words, whether he has a permission or not. In this stage, Spring provides us with an Authorization component which is called AccessDecisionManager. What this helps us with is by providing us with an API.
Thanks to AOP, we can achieve Authorization. AOP decides whether a method call is permitted for the user that’s calling it.
How to setup Spring Security in a Spring application
In the Maven pom.xml file, paste the following:
<dependencies>
<dependency>
<groupId>org.springframework.security</groupId>
<artifcatId>spring-security-web</artifactId>
<version>4.2.3</version>
</dependency>
<dependency>
<groupId>org.springframework.security</groupId>
<artifactId>spring-security-config</artifactId>
<version>4.2.3</version>
</dependency>
</dependencies>